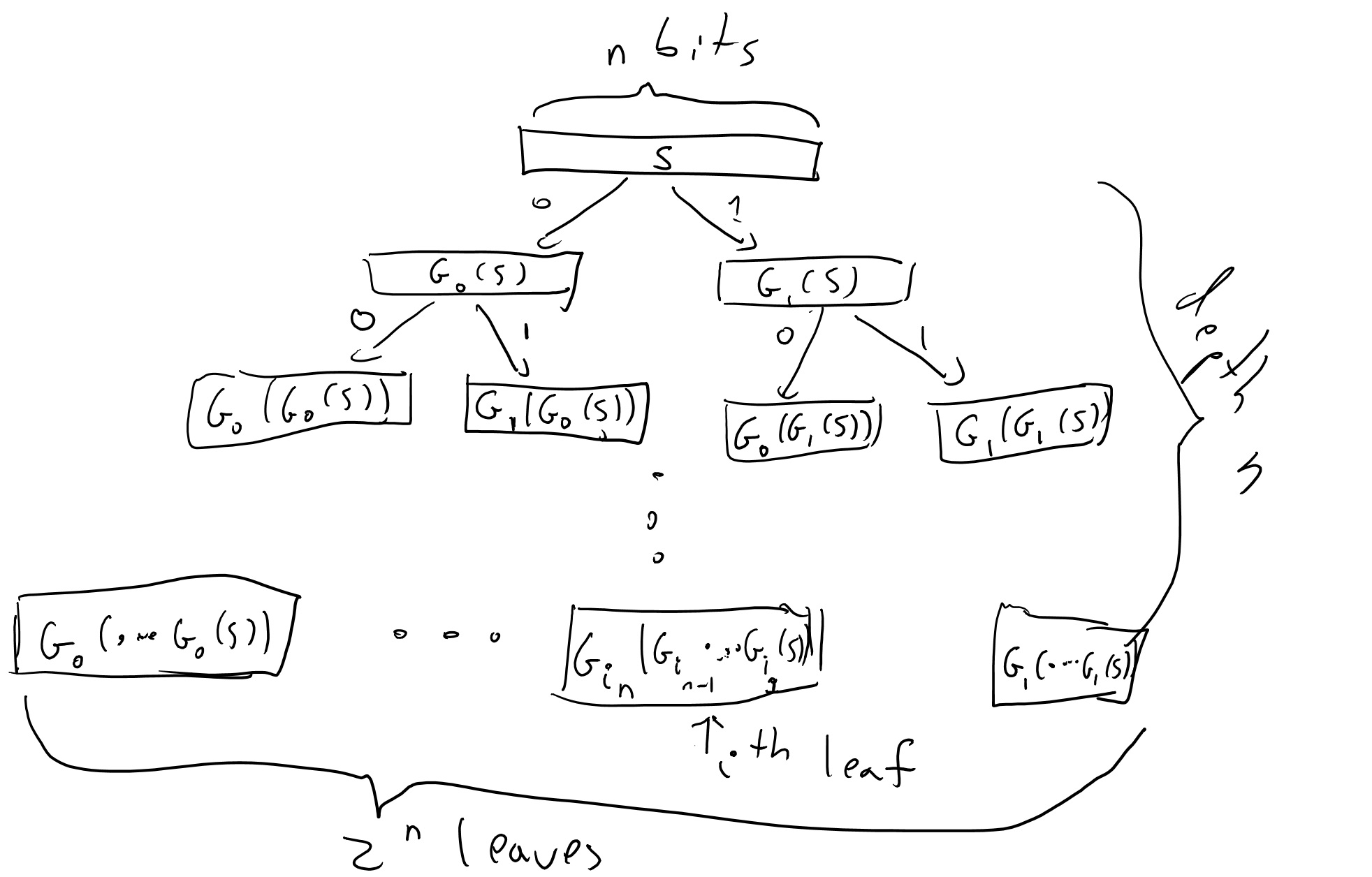
Flow chart for BEACH pseudo-random number generator. Here, C(B, x) is... | Download Scientific Diagram
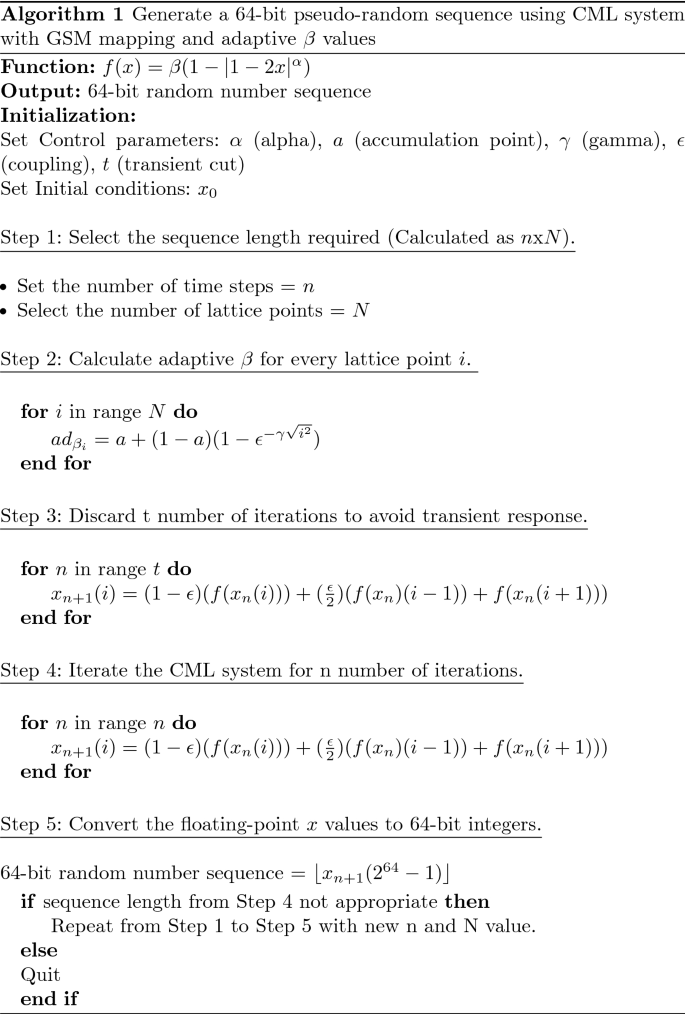
A novel pseudo-random number generator for IoT based on a coupled map lattice system using the generalised symmetric map | SpringerLink
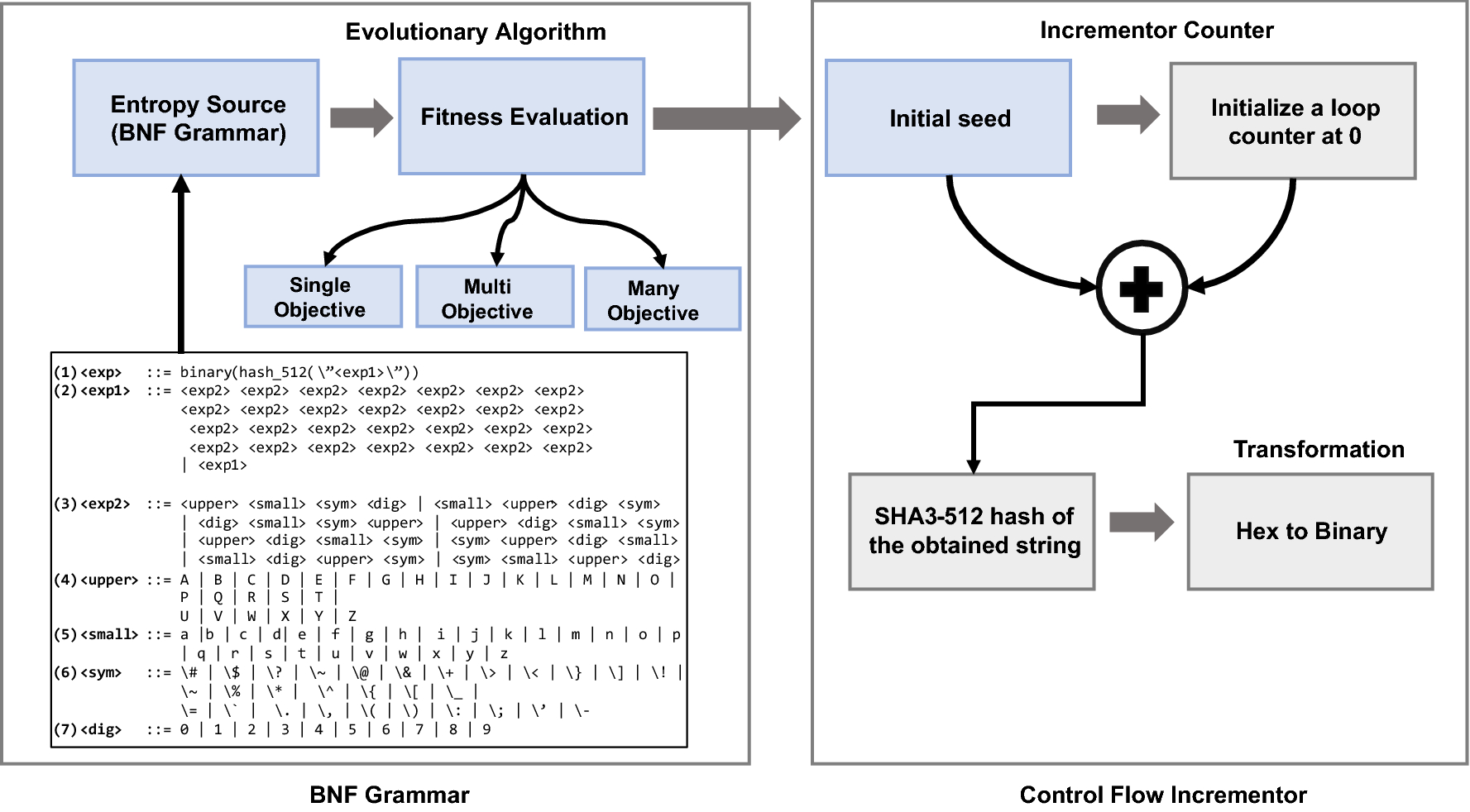
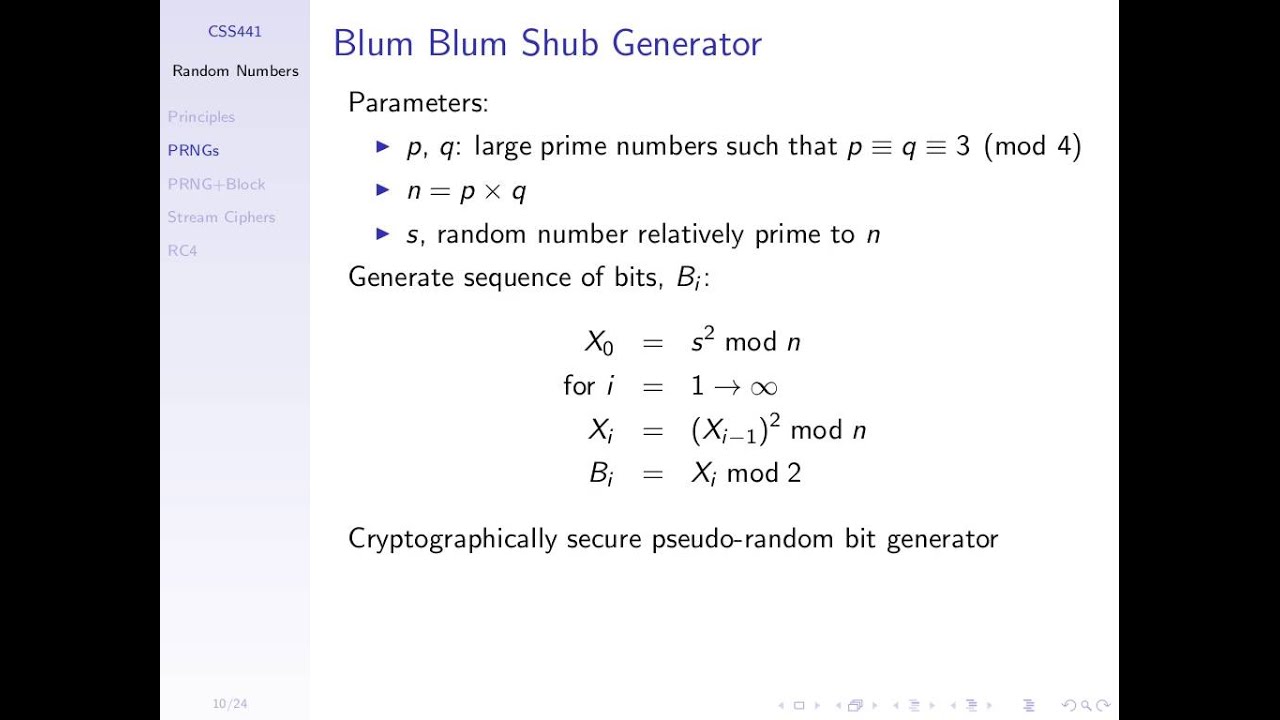
Design of a cryptographically secure pseudo random number generator with grammatical evolution | Scientific Reports

Flow chart for BEACH pseudo-random number generator. Here, C(B, x) is... | Download Scientific Diagram
How random is pseudo-random? Testing pseudo-random number generators and measuring randomness | Code crumbs, by Clément Pit-Claudel
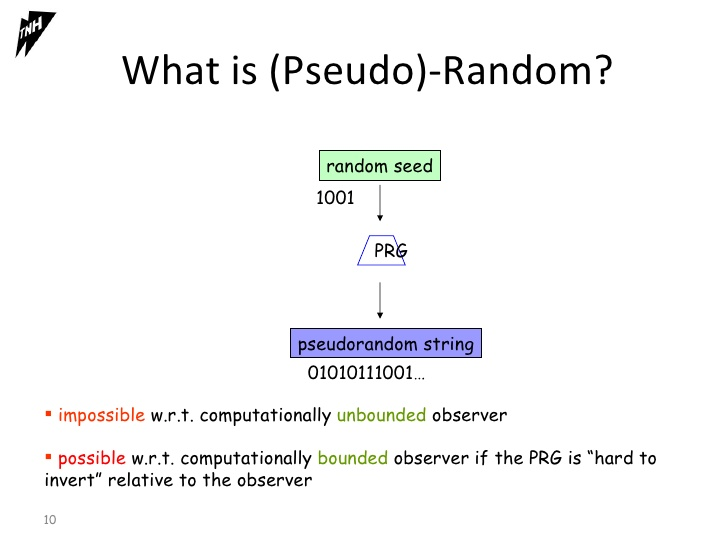
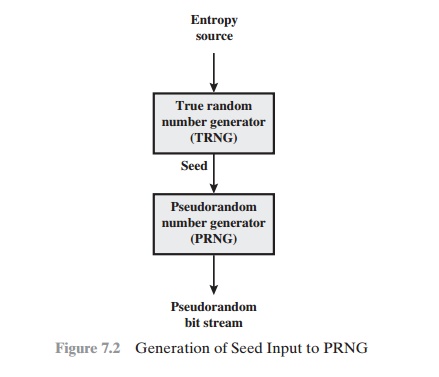
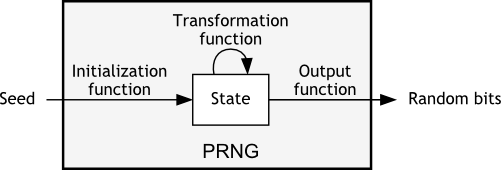
Working mode of Pseudo-random number generator (PRNG). PRNG contains... | Download Scientific Diagram